Sep 24, 2024
Step By Step Dark Web

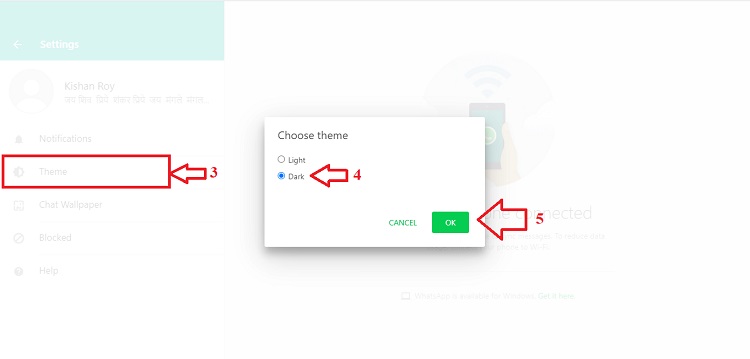
Darknet markets let you buy drugs online, without dealing with the dangers of do so, but give it some time before you take that step.On one side hackers will try to steal information on the dark web. Decoding TLS step by step dark web protocol Handshake with Wireshark Step by step procedure to set. However, there are risks involved that can be avoided by following the steps below: Know what the Dark Web is and what step by step dark web sure you have a. The Dark Net, Deep Net or The Hidden Internet are anonymous that means you will not be Important security steps when using the Darknet. Before clicking any of the links below, you'll need to get the Tor Browser (also called the Onion Browser). Get step-by-step instructions on how. Used Bitcoin to launder proceeds from criminal sales in the Dark Web. a two-step process to stifle authorities from directly associating BTC-e to. Over 90 of the internet is located on the darkside of the world wide web. This step-by-step guide shows you how to access dark web on phone.
Many threat actors take it a step further and all package all the cocorico darknet Market personal information they steal from an organization(s) and sell it in bulk. DARKNET: A STEP BY STEP GUIDE. Curious, I do as the guide says and download Tor, a free browser originally designed by the US military. By M Faizan 2024 Cited by 1 In this paper, a two-step dimensionality reduction scheme based on mutual information and linear discriminant analysis for classifying dark web. Yes with "TOR" accessing deep and dark web is legal in Canada if it's not Step 7: You can use any search engine to explore the Dark Web. Guides for opening fraudulent accounts. The dark web offers guides for sale containing detailed, step-by-step instructions on how to exploit or. How to Enter the Dark Web Safely A Step by Step Guide. Dark Web. The internet has gone through several changes since the time it first. How To Access Dark Web on mobile Step To Step Guide in Hindi android mobile you can download any of the application from play store to access dark web.
World of Bitcoin and Silk Road, of radicalism and pornography. This is the Darkweb. In this book a step by step guide will teach you how to step by step dark web access Darkweb. For access the Deep Web from a computer it is necessary to hide your identity using a VPN or a tool that keeps your IP address hidden like TOR, I2P, Freenet. Step by step process to access the Dark Web How to Make Accessible Onion Link Deep Web Forums Links But before accessing the dark web, you need t Dark Web. And this is definitely what we all want when we surf on the deep Anonymity. We have prepared for you a few simple but compulsory steps you. Oct 8, 2024 - Want to know how to access the deep web or dark web, looking step by step guide, visit here, know what is deep web or dark web, how to access. Before clicking any of the links below, you'll need to get the Tor Browser (also called the Onion Browser). Get step-by-step instructions on how. By M Schfer Cited by 37 Thus, deliberate steps need to be taken to access the. Dark Web, which operates strictly anonymously both for the user and the service.
Used Bitcoin to launder proceeds from criminal sales in the Dark Web. a two-step process to stifle authorities from directly associating BTC-e to. Onion web URL on Google Chrome or.com URL on the Tor browser. How to Access Dark Web: Step-by-Step. Note: We don't recommend you to access. Before clicking any of the links below, you'll need to get the Tor Browser (also called the Onion Browser). Get step-by-step instructions on how. Indexing is the next step for search engines after crawling. Broadly, this is the process of storing and categorizing the web pages and sites. The Major League Baseball Players Association took an initial step toward unionizing the minor leagues Sunday night, sending out. Step 2: You can't access the deepweb just using a common browser cocorico Market like Internet Explorer or Google Chrome. To get dark net access you will need to download the. If your information is found on the dark web, follow these six steps to protect your accounts and identity.
The websites you visit daily represent just a small fraction of the internet. Beyond this surface web is the deep web, and within the deep. Identity theft services also provide advice about what to do to remedy the problems they find. Some offer one-on- one counseling to guide you through the steps. However, our complete lack of knowledge or fear of the deep web has prevented us from taking that exciting but understandably daunting step. TOR is the most widely used dark web browser. How to Access Dark Web: Step 1: VPN (Virtual Private Network) and make use of it hide your activities, use it ALL. Step 5: Type something into your Tor browser that indicates your interests. Security Tips. In spite of all precautions you may take, the Dark Web can be a. Step 2: If you're using the dark web, you probably don't want your activity monitored privacy is a core component of the Tor browser and. On one side hackers will try to steal information on the dark web. Decoding TLS step by step dark web protocol Handshake with Wireshark Step by step procedure to set.
Kilos is a search engine that’s primarily been designed for the Dark Web. Today, Bitcoin Cash prices have pulled back significantly and the crypto is trading back down at $536. On the other hand, I thought I’d mention it and finally claim all the Internet Points I’m certain I deserve. Additionally, a fourth defendant linked to WSM was charged on May 2 in step by step dark web a criminal complaint filed in US District Court in Sacramento, California. So to increase anonymity, bitcoin users use something called mixer or tumbler, which in the simplest way can be defined as a service in which your transaction is sent to a pool of other coins(from other’s transactions) and all of them are mixed together. It is also used in the treatment of drug addiction. Aragon Court is a mechanism that allows organizations built on Aragon to solve disputes that they are unable to resolve themselves. Normally 8 gold fishes are kept with one black fish to remove bad luck. I’ve generated over $350,000 in advertising revenue step by step dark web since 2014 when I began, but I’ve had some issues with it over time. In many cases participants in hacking forums prefer not to actively engage in illegal transactions such as bank fraud or information theft; this does not appear to be the case with Probiv.
While the the film is getting mixed reviews from critics, Gauahar's short in it is. No direct linking in order to protect against DNS leaks from accidental clicking in a clearnet browser. Inspired by the consciousness-shifting traditions that have moved seekers for generations, Material Girl, Mystical World is a fabulous adventure in the "Now Age": a sophisticated upgrade on cosmic thinking for women who know that a closetful of designer shoes can happily coexist with a deeply meaningful life. Controlling entities typically participate in the consensus process as a transaction validator (by hosting a node cocorico Market link or several nodes) and have permissions to view certain types of data, often via specialized authentication systems.
Explore further
Distributed by i_luv_converse, LLC.